What Makes Humans Click? The Psychology of Phishing
Let’s jump into a bit of the psychology behind how hackers get us to click phishing emails. The threat of phishing has been well documented and known for years, but this is still one of the most successful ways for hackers to gain access to our data. So, we are asking the question why? Why does this tactic still work?
First, some quick brain science. This is super basic but it’s relevant, I promise.
Fact: The frontal lobe of your brain allows you to process and think about emotion and is consciously controlled by you.
Fact: The amygdala is the alarm sounder. When it interprets data as a threat, it sounds the alarm, triggering the avalanche of well-orchestrated neural processes that are almost instantaneous. We know of this as the fight or flight response.
Fact: Fight or flight is useful for evading dinosaurs and outrunning apartment spiders but totally useless when dealing with email.
Fact: The emotional brain is both quicker and stronger than the logical brain. Emotions, like fear and urgency, sidestep the frontal lobe and smack us right square in the amygdala.
Amygdala Hijack
This is otherwise known as hi-jacking your amygdala and it happens super-fast. Daniel Goleman coined this term based on the work of neuroscientist Joseph LeDoux. You see, Joseph demonstrated that some emotional information travels directly to the amygdala without engaging those higher brain regions that help you see logic and reason. The amygdala hijack is an immediate, overwhelming emotional response. Why is this relevant to IT you might ask? Well, when it comes to hackers trying to get access to your information, a successful tactic is to just introduce a psychological stressor, say in the form of a threatening email…
and then sit back and wait for it… (click). Before you know it, instead of really reading that email and carefully reviewing the link, you’re clicking with abandon like some sort of spazzy click dancer, click dancing at a click festival.
Consider that in less time it takes to rinse out your cereal bowl, someone can hi-jack your brain.
How to Prevent It?
Train like a ninja. Or, decide that you can’t totally get past thousands of years of evolution and instead, focus on preventing the aftermath with the 6-second rule. Waiting for 6 seconds for the brain chemicals that cause the amygdala hijack to diffuse away is a place to start. This means when you read an email that compels you to stop, drop and roll, BEFORE clicking on ANY link, ask yourself-
- What is the email trying to get me to do?
- How is it trying to get me to do it?
Once your logical brain catches up to your emotional brain, you are able to use logic to explore the email in more depth to see if it is valid. For more info on how to identify a phishing email, check out this video.
When Emotion Takes Over, We Click the Link.
We were curious to find out which emotions hackers typically exploit to get us to click and found that there are five primary scenarios that are the most effective.
Stress- Imagine you’re behind schedule or just desperately trying to get out of the office. Your jaw is clenched and you actually growl as that last email pops into your inbox. At this point, you’re driving to get finished up with that last task. You’re also going fast and not paying attention. This is like the speed limit. The faster you go, the more likely you are to run into trouble. Slow your roll and focus. Speeding through your email is not worth paying the fine to remediate the email breach you’re about to cause by clicking on a malicious link.
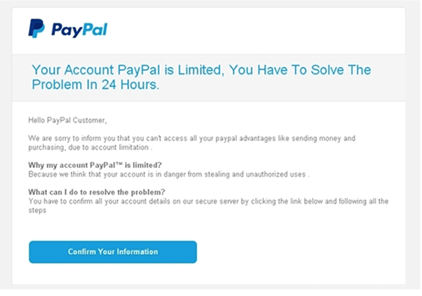
Fear- “Do this now or else…” Fear is a powerful motivator and arguably, when it comes to social engineering, the most commonly manipulated emotion.
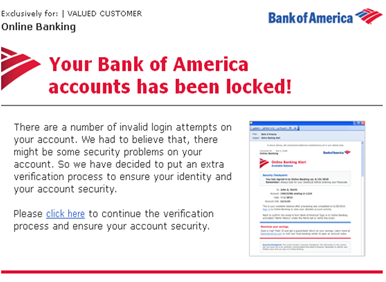
Emails that inspire fear and phishing links go hand in hand. Threatening police action, threatening to withhold money or lock your bank accounts are common. So are emails that prey on your fears of forgetting something, fear that you’ve done something wrong, fear that there’s something urgent you’re missing, fear that you’ll lose your job if you don’t do something. Fear makes us click.
Over Confidence– Humans are usually overly optimistic when evaluating our ability at intellectual tasks: otherwise known as ‘illusory superiority’ bias. This also means we’re overly optimistic regarding our abilities to recognize phishing emails. Just know that no matter how computer savvy you are when someone hijacks your amygdala, none of that higher brain function is in play. Oh, and if you think you can’t be phished read this.
Greed- To claim your millions, click here! Remember, if it’s too good to be true, don’t click. Out of 2000 people surveyed, “when asked if they had ever experienced any feelings of guilt after purchasing an expensive item, 56% of the people reported feeling either “extremely guilty” or a “little bit guilty,” a feeling that was particularly prevalent with millennials ages 25 through 34 (73%).” Finding a bargain lets us enjoy our expenses minus some of the guilt. Do not be manipulated by an unbelievable price drop on an item you’ve been eyeing. It probably is too good to be true.
Hierarchy and Authority – Research shows that people tend to comply with requests from authority figures. Handy for crowd control but not so much for managing ye ‘ole inbox. Hacker’s often use this tactic to ask a lower-level employee to complete a task, not ask questions, and to do it quickly. The best thing to do in this situation is to get in contact with the individual who sent the email in another way other than email. Calling is best, but a quick text is good as well. Hopefully, the CEO at your company would never randomly ask you for a wire transfer without any context and you have a process outlined for this process. But the pressure from wanting to please your boss might cost you more than you might think.
For all of these emotional situations, it’s necessary for us to be mentally be present. Understand that hackers are now experts in social engineering. They know what to say to trigger your emotional brain and often use a variety of tactics at once. We’re surrounded by news headlines, advertisement and articles all vying for our limited attention and precious time. It’s easier than ever to trip into a phishing scam.
Good Email Hygiene
- Assume that there’s something phishy about every link in every email
- Pay attention
- What is the email trying to get you to do?
- How is it trying to get you to do it?
- Remember the 6-second rule.
For more tips on navigating cyberspace safely, visit our website. If you have encountered a security breach, especially within your work network, don’t hesitate to reach out to our team and we will help you find your way back to security. Until then, we wish you and your amygdala’s 6-seconds of space to respond and safe emailing!